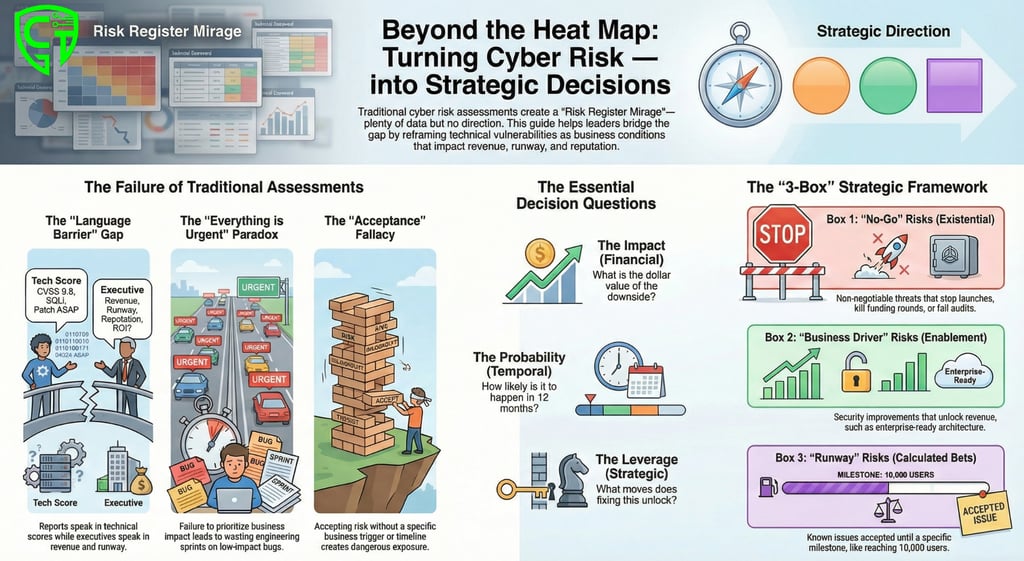
The Risk Register Mirage: Why Your Cyber Assessments Aren’t Driving Decisions (And What to Do About It)
Most cyber risk assessments create noise, not direction. Learn how to bridge the gap between technical checklists and strategic business decisions in AI, Fintech, and Healthcare SaaS
Fridrick Charles
2/24/20264 min read
Bridging the gap between compliance checklists and the strategic business decisions that keep your SaaS startup alive.
Reading Time: 4 Minutes
Target: CEO, CISO, CTO, Founder
You’ve just received the latest cyber risk assessment. The spreadsheet is immaculate. The heat map is glowing amber. The risk register lists forty-seven distinct vulnerabilities.
But as you stare at the findings, a sinking feeling sets in. You have no idea what to do next.
Should you halt the rollout of the new feature to patch a "High Risk" library? Should you burn through another $50k of runway to hire a DevSecOps engineer? Or should you accept the risk and hope the VCs don't ask too many questions during the due diligence call next week?
If this sounds familiar, you aren't alone. You are experiencing the "Risk Register Mirage." It looks like data, but it offers no direction.
For founders, CEOs, and CTOs of seed-stage and scaling SMBs in AI, Healthcare, and Fintech, this gap is existential. You operate in a high-trust, high-regulation environment with the runway of a startup. You cannot afford to waste time on noise. You need decisions.
Here is why most cyber risk assessments fail you—and how to bridge the gap between technical noise and strategic action.
The Problem: The "Check Engine Light" With No Mechanic
Traditional risk assessments are designed for compliance, not decision-making. They are backward-looking. They count vulnerabilities like notches on a belt, telling you that something is broken, but not why it matters to the business.
For a decision-maker, this creates three critical failures:
1. The "Language Barrier" Gap
The assessment speaks in CVSS scores (Common Vulnerability Scoring System) and technical exploits. You speak in revenue, runway, and reputation. When a report says, "Critical cryptographic implementation flaw in auth module," you need to hear, "We may lose the ability to secure patient data, triggering HIPAA fines and losing enterprise clients." If the translation doesn't happen, the report gets filed and forgotten.
2. The "Everything is Urgent" Paradox
Risk registers love to list everything. They rarely prioritize based on business impact. When a Healthcare AI startup sees a "High Risk" next to a minor API issue and a "High Risk" next to a potential data leak that could kill an FDA approval, the scale is broken. If everything is priority one, nothing is priority one. You end up wasting engineering sprints on low-impact bugs while strategic risks fester.
3. The "Acceptance is Not a Strategy" Fallacy
Most assessments end with "Risk Accepted." But why? In a startup, we take calculated risks every day to move fast. However, "accepting" a risk without understanding the business trigger (e.g., "We accept this until we close the Series A, then we fix it") is dangerous. It leaves the business exposed without a timeline or a trigger for action.
The Bridge: Risk as a Business Dial, Not a Technical Switch
To make a decision, a leader needs to know three things:
The Impact: What is the dollar value of the downside?
The Probability: How likely is it to happen in the next 12 months?
The Leverage: What strategic moves does fixing this unlock?
If your cyber risk assessment doesn't answer these three questions, it's not a decision-making tool; it's just paperwork.
In the high-stakes world of Fintech (where a breach kills trust overnight), Healthcare (where patient safety and regulations collide), and AI (where intellectual property is the entire company valuation), we need to reframe the conversation.
We need to move from Vulnerability Management to Executive Risk Dialogue.
How to Bridge the Gap: The "3-Box" Method
As a leader, you don't need to see the 47 vulnerabilities. You need to see them sorted into three boxes. Insist that your security team or vendor presents data this way:
Box 1: The "No-Go" Risks (Existential Threats)
These are the non-negotiables. If these are not fixed, you cannot launch, you cannot close the next round, or you are guaranteed to fail a compliance audit (SOC2, HIPAA, GDPR).
Decision: Allocate resources immediately. This is a "stop the line" issue.
Box 2: The "Business Driver" Risks (Strategic Enablement)
This is where security becomes a revenue generator. Perhaps fixing a specific architecture allows you to support multi-tenancy for enterprise clients. Perhaps hardening the API is the final requirement to sign that Fortune 500 pilot.
Decision: Schedule this into the product roadmap as a feature. It isn't a security tax; it is a sales enablement ticket.
Box 3: The "Runway" Risks (Calculated Bets)
These are the "known unknowns." They are real, but they don't threaten the immediate survival or the next major milestone. You might decide to accept these for now.
Decision: Explicitly accept them, but tie them to a trigger. ("We accept this risk until we hit 10,000 users, at which point we will remediate.") This prevents technical debt from spiraling out of control.
The Bottom Line for SaaS Leaders
You are building a high-velocity machine. Whether you are an AI startup protecting proprietary models, a Fintech handling direct deposits, or a Healthcare SaaS managing Protected Health Information (PHI), your security posture should accelerate your business, not slow it down.
Stop accepting risk assessments that give you a headache instead of a roadmap.
You need a security partner who understands that a vulnerability is just a technical symptom, but a risk is a business condition.
Ready to turn your risk register into a growth roadmap?
If you are a founder or executive at an AI, Healthcare, or Fintech SaaS company tired of drowning in spreadsheets instead of making confident decisions, let's talk.
We don't just hand you a report. We facilitate a 15-minute Executive Risk Dialogue to map your technical reality to your business goals, runway, and growth milestones.
[Click Here to Book a Scoping Call] — Let’s bridge the gap between security noise and strategic decisions.


Decision-focused cybersecurity for leaders under pressure.
Follow us
Engagement Model
Regional Office
1st Floor, No 1 Manickavasagar Street, Viswanathan Nagar, Muthialpet, Pondicherry, INDIA
Quick Links
© 2025 FRIDRICK CYBER TECH. All rights reserved. | Decision - focused cybersecurity
Legal
Recognized at the Startup Clarity Challenge 2026




