Compliance Passed. Breach Happened. Now Who Owns the Risk?
Blog post descAI SaaS, HealthSaaS, and FinTech SaaS companies are clearing audits—yet breaches still happen. This article confronts the uncomfortable leadership gap between compliance and real risk ownership, exposing the decisions founders and boards avoid until an incident forces accountability.
INSIGHT
Fridrick Charles
3/2/20262 min read
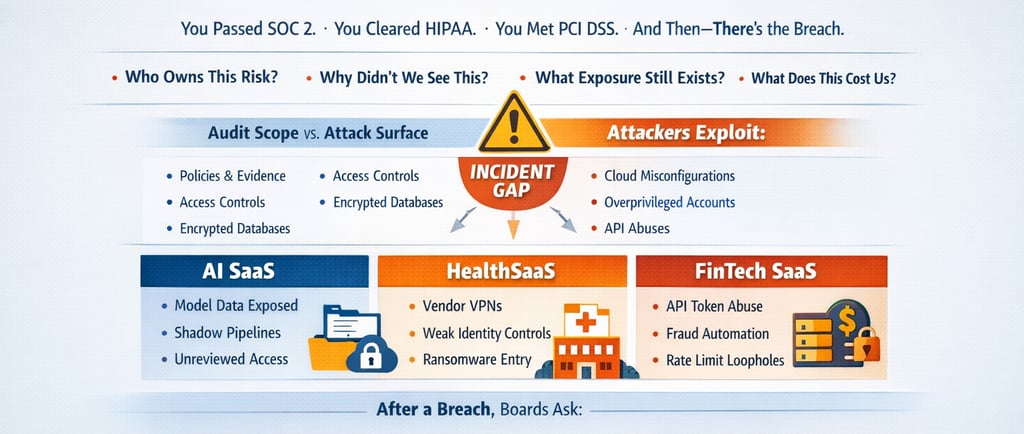
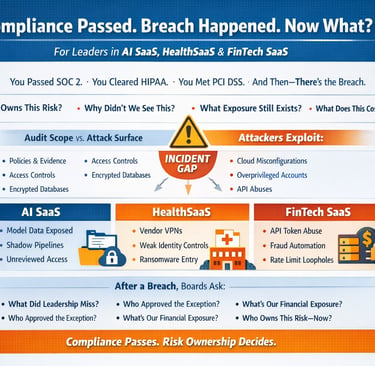
For AI SaaS, HealthSaaS, and FinTech SaaS Leaders
You passed SOC 2.
You cleared HIPAA.
You met PCI DSS.
Three months later, there’s an incident.
Now the board isn’t asking about your audit report.
They’re asking:
Who owns this risk?
Why didn’t we see this?
What exposure still exists?
What does this cost us?
Compliance answers none of those.
Compliance Validates Controls.
Attackers Exploit Assumptions.
Audits confirm:
Policies exist
Controls are designed
Evidence is sampled
Requirements are met
Attackers target:
Cloud misconfiguration drift
Identity sprawl
API abuse
Over-permissioned service accounts
Third-party integrations outside the scope
Product velocity exceeding governance
The gap between those two realities is where incidents occur.
That gap is not technical.
It is executive.
AI SaaS: When Innovation Outruns Governance
AI SaaS companies often operate under frameworks like SOC 2 or ISO/IEC 27001.
Controls are documented.
Access policies exist.
Change management is defined.
But model training pipelines evolve weekly.
New data ingestion paths are created.
Temporary API keys become permanent.
Storage buckets are spun up outside formal review.
When exposure happens, leadership says:
“We were compliant.”
That’s not what regulators, customers, or investors evaluate.
They evaluate:
Why did governance not match product velocity?
The decision most AI SaaS founders avoid:
Do we align release speed to risk oversight capacity?
HealthSaaS: Compliant on Paper. Exposed in Practice.
Health platforms align with Health Insurance Portability and Accountability Act requirements.
Encryption is in place.
BAAs are signed.
Annual risk assessments are performed.
Yet ransomware rarely enters through encrypted databases.
It enters through:
Third-party clinical integrations
Legacy VPN access
Overprivileged service accounts
Weak identity lifecycle management
After impact, regulators don’t ask:
“Did you have a policy?”
They ask:
“Why was privileged access not continuously governed?”
The avoided decision:
Who owns identity governance across product, IT, and vendors?
If the answer is unclear, exposure accumulates quietly.
FinTech SaaS: PCI Passed. API Exploited.
FinTech companies validate controls under PCI DSS.
Cardholder environments are segmented.
Encryption is validated.
Access is restricted.
But fraud rarely attacks storage.
It attacks logic.
Token misuse
Refund workflow abuse
Weak rate limiting
Long-lived API credentials
Business thresholds overriding risk thresholds
The audit passes.
Fraud loss escalates.
Board question:
“Did we accept this exposure knowingly?”
Silence here is not operational.
It is a governance failure.
Before the Audit vs After the Incident
Before audit
Are controls documented?
Is encryption implemented?
Do we have evidence?
After incident
Who approved the exception?
Why wasn’t this environment monitored?
What is our real financial exposure?
Who owns third-party risk?
What did leadership know?
Compliance answers the first list.
Risk governance answers the second.
Most SaaS companies optimize for audit success.
Boards care about survivability.
The Leadership Decision Being Avoided
Compliance is a minimum threshold.
Risk ownership is a leadership obligation.
The real questions are:
What level of breach impact are we financially prepared to absorb?
Is cyber risk translated into a balance sheet impact?
Are we measuring attack path exposure, not just control existence?
Who signs off on residual risk — explicitly?
If those answers are not documented at the executive level,
Compliance is not protection.
It is delayed.
What Changes After a Breach
After impact, companies demand:
Attack path mapping
Privileged access exposure analysis
Cloud configuration drift visibility
Third-party risk quantification
Financial impact modeling
Board-level risk reporting
In other words:
They move from compliance validation
to decision-grade risk intelligence.
The cost of making that shift after damage
is always higher.
Financially.
Operationally.
Reputationally.
A Direct Question for Leadership
If your company passed compliance this year:
Who is accountable if a breach occurs next quarter?
If the answer is “the security team,”
You have delegated risk.
You have not owned it.
And delegated risk is what boards examine
after failure — not before.
About Fridrick Cyber Tech
We work with AI SaaS, HealthSaaS, and FinTech SaaS leadership teams to:
Quantify financial cyber exposure
Map real attack paths across cloud and product environments
Define executive-level risk ownership
Translate technical exposure into board-ready decisions
Not to pass audits.
But to decide risk consciously.


Decision-focused cybersecurity for leaders under pressure.
Follow us
Engagement Model
Regional Office
1st Floor, No 1 Manickavasagar Street, Viswanathan Nagar, Muthialpet, Pondicherry, INDIA
Quick Links
© 2025 FRIDRICK CYBER TECH. All rights reserved. | Decision - focused cybersecurity
Legal
Recognized at the Startup Clarity Challenge 2026




